Resources
Why Privacy Policies Aren’t What They Seem: Leveraging Global Threat Intel to Keep Your Mobile Data Safe
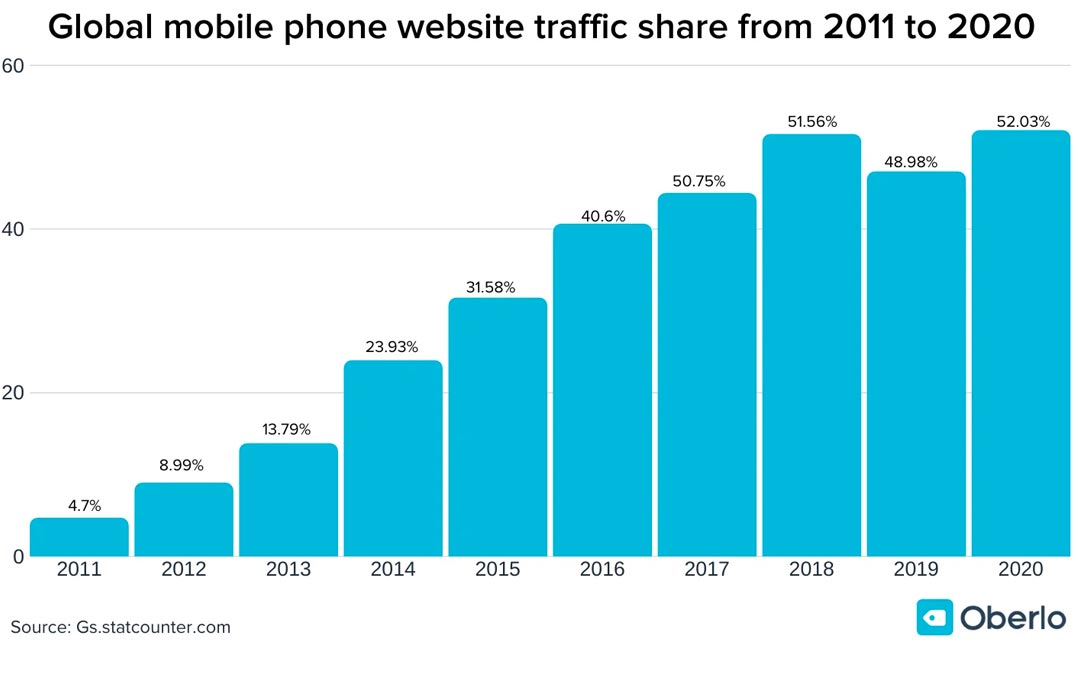
Cyber criminals are more active than ever, which means protecting your data has never been more important. One in three websites related to the outbreak of coronavirus launched this year are scams. Of the 300,000 websites related to the virus launched globally since...
News & Announcements
No Results Found
The page you requested could not be found. Try refining your search, or use the navigation above to locate the post.

The Human Firewall
Traditionally firewalls have been considered the edge of a network perimeter, and the first line of defense against cyber attacks. Firewalls, however, can only be as effective as the weakest link in the security chain. Often, the weakest link is on your payroll. This...

Andromeda command-and-control on SourceForge
by Seth Elo We are no strangers to online code repositories and social media being abused for malicious intents. Attackers will use services like these in hopes to make their malware harder to detect, easier to manage, and give their bot’s C2 communications a lower...
Petya Ransomware
In the last half of 2016, the rise of ransomware became a force to be reckoned with, with several new variants being discovered weekly. That trend has shown no signs of stopping in 2017. With one of the latest variants – called Petya by parts of the security community...

Coming To a Break Room Near You: Point-of-sale malware
Coming To a Break Room Near You: Point-of-sale malware by Noah Dunker At about 6:00 AM on July 4th, 2017 RiskAnalytics’ ThreatSweep platform identified a break room vending kiosk at a customer’s office that had been infected with a point-of-sale malware family that’s...
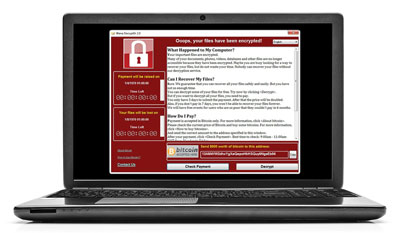
WannaCry Ransomware Outbreak
by Noah Dunker A new variant of the WannaCry ransomware family, “WanaCrypt0r 2.0,” was discovered in the wild sometime around 8:00 AM GMT, Friday, May 12, 2017. This “worm” variant of WannaCry spreads by using a recently-fixed critical-severity Microsoft...
